The concept – and resulting belief system – of Advanced Persistent Threats (APT) as an uncommon and/or unique type of attack that only focuses on high value data in a subset of industries is a dangerous one. Classifying threats as APTs is a convenient way of minimizing the reality of the attacks and dismissing them as unlikely. A better way to think about the threats facing companies that have any internet-facing assets is as a multi-stage attack.
Myth: APT’s only target key industry verticals…we aren’t in those so we’re probably not a target
SearchSecurity – amongst other well read industry sources – specifies in its definition of APT that, “APT attacks target organizations in sectors with high-value information, such as national defense, manufacturing and the financial industry.” However, this narrow view of APT is perilous. To begin with, attacks that fall under the APT banner are not relegated to specific industry verticals. They don’t only target high-value data. Multi-stage attacks affect over 450 unique SIC codes in Alert Logic’s customer base alone, based on the 18 months of data we analyzed for our most recent Cloud Security Report.
Myth: APT’s require advanced coding skills so there may not be as many hackers using these techniques
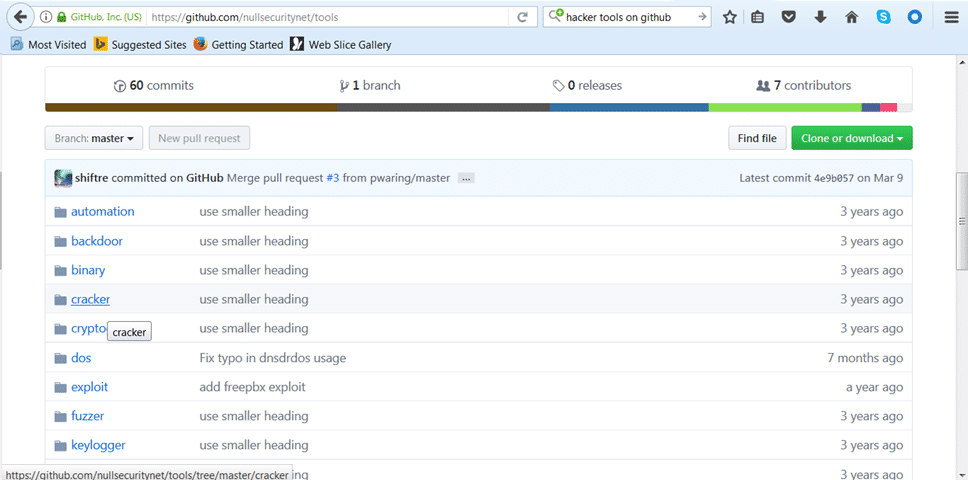
In most cases, the exploits and techniques used by bad actors are really not all that advanced. With today’s availability of automated tools that enable non-developers (and casual “hackers”) to string together access and evasion steps, teams should not assume there is a lower risk. The supply side of the bad actor’s tool-kits is increasing and thus the pool of players who are getting into the business is increasing as well. Entry and evasion tools can be accessed as easily as grabbing them off of Github.
Large scale, automated reconnaissance efforts can now be completed in a few clicks using publicly available methods like Google dork queries and open source vulnerability scanners. The data behind the 2017 Cloud Security Report shows high usage of packaged recon tools for malicious intent with OpenVAS (43 percent), SIPviscious (14 percent) and ZmEu Exploit scan (10 percent) taking the majority share of voice amongst attackers in their recon efforts.
Myth: End-points are the entry point for APT’s that I should focus on
There is also a pervasive belief that endpoints are the main entry point for APTs. The myth is that spam and spear phishing attacks are the primary method of compromise. While these entry techniques are absolutely in use, its worrisome that other entry points are often not being discussed often. Vulnerable web applications or cloud workloads are among the top entry points we’re observing – and those topping the list of breach sources per Gartner, SANs, and Verizon. This meme can lead to teams over-rotating on endpoint security and underfunding web application defenses.
In both the recent Equifax and the many Yahoo data breaches it appears attackers have relied on basic entry and evasion techniques that use web applications as the main vector for compromise, with the Equifax data breach reportedly the result of an unpatched vulnerable web application using Apache Struts. Alert Logic observes a majority of multi-stage attacks using web application vulnerabilities as the initial point of compromise with recon and injection stages used in over 45 percent of security incidents analyzed over an 18-month time period.
Persistent vs Smash-and-Grab
Persistent is probably the only word in the term Advanced Persistent Threat that is useful for defenders to root themselves in. Multi-stage attacks aren’t smash-and-grabs. They can occur over days – even weeks or months.
If you’re going to get compromised, it sounds much more impressive to be compromised by an Advanced Persistent Threat (APT) than just plain ordinary malware or a simple exploit. Organizations would prefer to believe that they were specifically targeted by attackers of above average skill, armed with exceptional zero-day exploits. It takes some of the sting out of getting compromised. The reality, however, is that most attacks classified as APTs aren’t all that special or advanced, and continuing to think of them that way puts organizations at greater risk.
“Multi-stage attacks” is a safer, more actionable description of the threats we all face today
Given the reality of the threat landscape, though, shouldn’t we be toppling the pedestal that is propping up the misnomer of APT’s? It’s too easy for teams to say, “We are not a target,” or, “We have layers of defenses for our perimeter and endpoints so we are set,” or say, “There can’t be that many hackers out there that can do this stuff, so the risk is low.” If teams start to think about the more pragmatic, and more real threat type that is prolific – the multi-stage attack – they may start focusing on closing the gaps sooner and with more accuracy.
Learn more in a webinar
Join Scott Lambert, head of Threat Intelligence for Alert Logic, and myself to learn what techniques attackers are leveraging, which environments are most at risk, and what actual multi-stage attacks are comprised of. Make sure your attention is focused on the threats that really matter.
Register now: Understanding Your Cloud Attack Surface.
Voice your thoughts and comments to this post. The more voices in the discussion the better.